As expected there is nothing too intersting here.
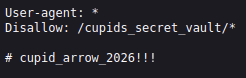
Next thing I like to do is check for a robots.txt file attached to the site.
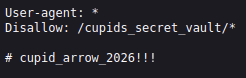
We did however find something interesting here. It is always a good idea to check this file.
Reviewing robots.txt during a web pentest is critical because it often reveals hidden directories, sensitive endpoints, or administrative paths that developers intended to keep out of search engines, but not necessarily out of reach from attackers.
From the looks of it. We have a directory to search and a possible password. We need to save both of these.
Next, lets run a directory scan. There are many options out there but i am going to use Gobuster this time.
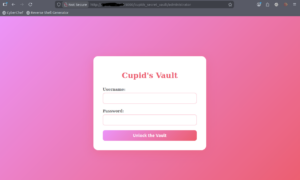
We did not find anything exciting using the main site. When we put in the directory we found in the robots.txt file though, we find an administrator page.

Now, we will look at this page.
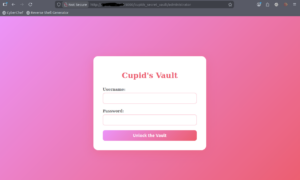
Here we find a log in page. Let’s try to use the possible password we found in the robots.txt file.
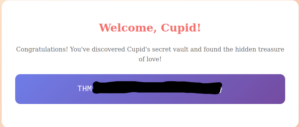
Using administrator as the username didn’t work, however if we use admin it does work.
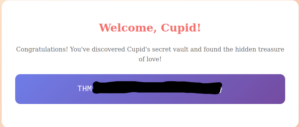
We found the flag! Now enter it in the room and submit your answer.
While this was a rather easy task to complete the methods used here can be extremely helpful when performing a real pentest.